This year has seen a noticeable surge of software vulnerabilities, with over 65,000 discovered in 2022 - an alarming 21% increase from the previous year. Making matters worse is hackers' consensus that organizations are failing to keep up as attack surfaces expand due to inadequate internal knowledge and expertise. To counterattack, most ethical hackers are brushing up on the fundamentals of the five phases of ethical hacking, which are:
Reconnaissance
Scanning
Exploitation
Maintaining Access
Covering Your Tracks
Without further ado, let's delve into each phase of ethical hacking in detail.

1. Reconnaissance
Ethical hacking begins with reconnaissance, also known as "footprinting," or "fingerprinting," or "information gathering." This is where you gather as much information about the target organization as possible.
This might include things like the IP address range, location, types of operating systems, technologies, and software versions used, system configurations, security measures already in place, user accounts, and passwords. In addition to the technical aspect, it is important to know who the target is and what they do.
The main goal of this stage is to really understand the target organization's systems and to have an extensive list of IP addresses that belong to them.
Common tools that are normally used to perform reconnaissance effectively include:
Using search engine directives
SEAT (Search Engine Assessment Tool): allows you to search multiple search engines at once.
Maltego: collects information about the target from public databases.
Why is reconnaissance important in ethical hacking?
To start with, thorough reconnaissance allows the ethical hacker to gain understanding of their target's technical structure, and this helps in later stages to identify the best method for gaining access to a network or system.
For instance, when you know that the target system is using Linux, then later on, you won't waste time looking for Windows exploits, but instead will focus on Linux-specific ones.
It also helps the ethical hacker find out if there is any sensitive information about the target organization that could be unknowingly leaked by employees or found on the internet. Additionally, this step can help create a password dictionary, which can then be used in attempts to break into systems.
Additionally, reconnaissance can include information gathering via social engineering techniques such as phishing emails, calls, or physical visits to gain access to restricted areas. By understanding how security conscious the employees are at a particular company in regards to sharing information with those outside of their organization, an ethical hacker can assess potential risks that might not otherwise have been identified.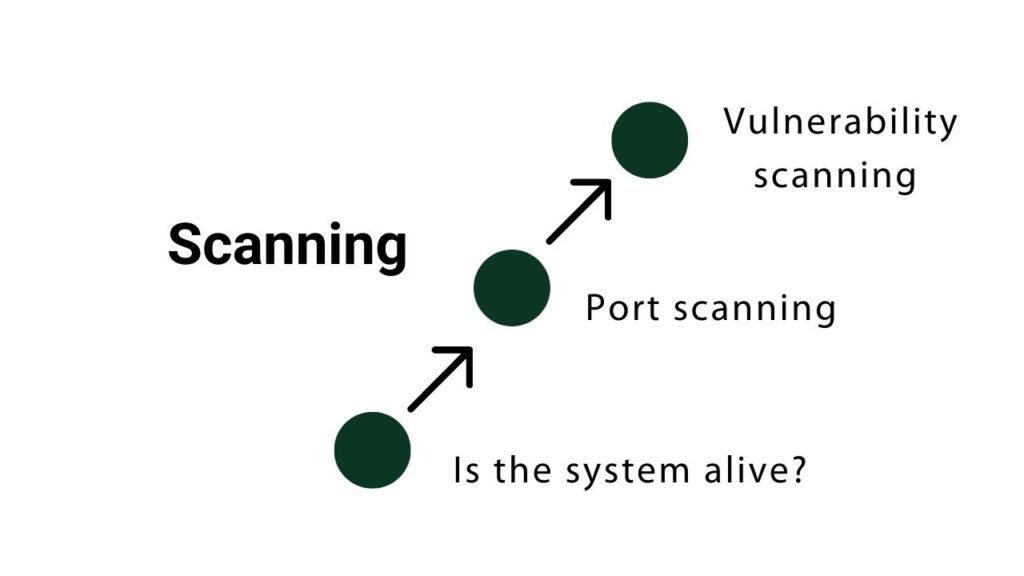
2. Scanning
The second phase of ethical hacking is scanning. This involves using different tools to see which systems in the target organization are turned on and what services those systems offer. You basically take the IP addresses that you found in the reconnaissance phase and see which ports are open on those systems.
Scanning involves three steps:
- Finding out if the target systems are alive
You need to know if the target systems can talk to your computer. To do this, a technique known as a "ping sweep" is used.
A ping sweep involves sending out an ICMP echo request packet to all IP addresses that belong to the target system, which will then return an echo reply packet if the target system is on, not restricted, and able to communicate with the computer that sent the request. This echo reply packet serves as confirmation that the target system can communicate with your computer.
Additionally, pinging a system or network tells you which devices or systems are on, how long it takes for packets to travel there and back, as well as what traffic was lost, so you can gauge how reliable the connection is.
After running a ping sweep, you'll know about all the devices in your target organization that your computer can talk to.
2. Port Scanning
Ports are like potential entry points or gateways into a system. Port scanning is analogous to knocking on the doors and windows of a house to find out where one can enter.
Every computer has a total of 65536 ports, and port scanning is a way to find out which ports are open. This also tells the ethical hacker what services the system provides. The most common tool used in port scanning is Nmap.
After you scan the ports, you should have a list of IP addresses, open ports, and services on the devices that belong to the organization you are pen testing.
3. Vulnerability Scanning
Vulnerability scanning is the process of looking for known security flaws in devices, like missing patches or misconfigurations.
This helps ethical hackers to further understand the target system, by seeing what "holes" attackers could potentially exploit. Some common vulnerability scanners are Nessus and NikTo.
Why is scanning important in ethical hacking?
By scanning, ethical hackers can identify which target systems are able to communicate with their own devices, the open entry points on those target systems, and the services they offer. Additionally, they can uncover any known or potential vulnerabilities that could be exploited.
3. Exploitation
Exploitation is the process of using the information gathered in the scanning phase to gain access to systems, networks or applications.
In this step, ethical hackers can take advantage of identified bugs, and misconfigurations on target systems by exploiting them. The goal of exploitation is usually to gain control over a system, but it could also be to acquire sensitive data, or to gain a better understanding of how an application works.
Ethical hackers use different tools in this step of the process. The most well-known tool is called Metasploit.
Metasploit is a penetration testing framework which allows ethical hackers to launch pre-defined attacks on target systems. They choose the attack based on the vulnerabilities they found in the scanning phase. Some examples of attacks are adding new users, opening a backdoor, installing new software, or changing settings.
Furthermore, since most organizations being pen tested have an online presence, it is not surprising that ethical hackers try to find ways to exploit web vulnerabilities.
This could include launching code injection attacks which could manipulate inputs or queries to the target web server or launching cross-site scripting attacks.
Also, exploitation could be breaking the system's passwords to get remote access to a system or get administrative access to a system. Common password crackers include Medusa and Hydra.
4. Maintaining Access
If, with the client's permission and consent, a penetration tester or ethical hacker requires access to a backdoor, this step is essential. Maintaining access is a step that serves as a proof of concept to show that an attacker could return to the target at any time.
To maintain access to an infiltrated system, ethical hackers use backdoors. A back door is malicious code that is uploaded on the target computer to allow a malicious attacker to bypass normal authentication, gain access to the system, and obtain full administrative privileges.
Generally, hackers leverage a single exploit to gain entry, and then they put in a backdoor so they can. The tools used for implementing back doors include the likes of NetCat, NetBus, and rootkits.
5. Covering Your Tracks
The final step of ethical hacking is covering your tracks. After the successful infiltration and exploitation of the target system, you should make sure to leave no trace behind.
Covering your tracks implies that you need to delete log files, disable audit trails, reset registry values, and clean up temporary files that may be used as evidence of your intrusion.
Additional Step: Reporting
This is the process of documenting and reporting your findings to the client. During this step, ethical hackers should be sure to include details about the vulnerabilities that were discovered and exploited, and provide recommendations to protect the target system from future breaches.
The report can be divided into three sections. The first section is the executive summary. This part should be written in a language that is easily understood by non-technical management. It includes your major concerns and how these vulnerabilities could hurt the organization.
The second section is the detailed view of your work. It should include more technical information for people who are experts, such as IT managers, IT auditors, and other security experts. They will use this information to understand the details of what you found and how to fix the issues.
The last section consists of all the raw output of the tools you used in the ethical hacking process. This should include all the screenshots, log files and evidence that was gathered during the engagement to help with further investigation or remediation efforts.
Final Thoughts
We ran through the five phases of ethical hacking so that you can get an idea of how to approach your next pen test. If you found this helpful and want to learn more, check out LinkedIn Learning’s ethical hacking learning path for beginners.